Data at rest, Data in Transit and Data in Use, these three terms we often hear when someone talks about data protection. This article explains why you should use file and folder Level encryption on top of full disk encryption. Let’s drive into detail of full disk encryption vs file and folder encryption.
Individual and business users want to take solace in knowing that if an attacker ever finds their documents, this “data at rest,” will be useless and unreadable.
Most data breaches are either due to insider actions, both intentional and accidental, or are intercepted while in transit. Both of these cases involve the proper operation of data storage devices.
Unfortunately, people often leave this data unprotected. Once an attacker has gained access to the remote file shares, it’s simply a matter of traversing directories, finding the files that he or she wants, and copying them.
What is Full Disk Encryption(FDE)?
In Full Disk Encryption technology, the whole disk gets encrypted using an encryption key. When the system starts, it prompts the user to provide an encryption key, and using that encryption key data is decrypted and the system boots and runs normally.
What is File System Level Encryption(FFE)?
With File level encryption, individual files and directories in the filesystem are encrypted by the filesystem itself. It does not encrypt the disk as a whole. Rather, encryption is done on filesystem level.
Using this encryption technology, we can efficiently encrypt and decrypt selected files and directories in the filesystem, where other not so important files and directories can remain unencrypted at the same time.
Full disk encryption
Sure, you could encrypt your entire hard drive, and you should! However, this is only one layer of a good security policy. Experts will tell you that it’s always a good idea to utilize multiple layers of security in case one fails. Your policy should have many layers, like an onion.
In the world of information security, experts refer to this concept as “defense-in-depth.”
The problem with relying on full disk encryption is that it was never meant to fit the use case of the machines that are hosting files online 24 hours per day. Typically, a user powers on a machine and enters the encryption key.
The entire drive is then decrypted, and is not re-encrypted again until the machine is powered off. If a user were to rip the hard drive out of the machine, the files contained on this fully encrypted drive would not be accessible to the attacker.
However, what if the attacker was able to compromise the machine hosting the files while it was powered on? Game over.
I don’t want to discredit full disk encryption, I merely want to state that it does not provide the level of protection that experts sometimes assume. A good analogy would be locking the door to your house, but leaving all of your jewelry and financial information prominently displayed on your dining room table.
Once someone bypasses the door lock, they have what they’re looking for. In this way, once the hard drive has been decrypted (when the system boots up and the encryption key is entered), user files are no longer safe.
How to stop thieves in their tracks?
Using Kruptos 2 Professional is analogous to storing your jewelry and financial information in a locked safe that only the owner knows the combination to. It’s an extra layer of defense, and an important one. While full disk encryption protects the user against theft of the hard drive, Kruptos 2 Pro, protects the user against unauthorized access.
Kruptos 2 Pro provides transparent and automatic file and folder encryption of individual files or folders at their inception and during view or editing of those files. Inherent and Krutpos 2 Pro encryption protects the data whether leaked, lost, or stolen.
Even more secure: Individual file and folder encryption
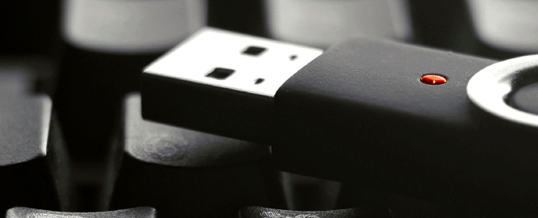
One mitigation to this threat is to encrypt individual files in such a way that an unauthorized user cannot decrypt them. As an example, let’s say that your file server houses both medical and legal documents. You want to make sure doctors cannot access legal documents, and that lawyers cannot access medical documents.
If you are using full disk encryption, you can’t guarantee this requirement. Once a machine is powered on and the encryption key entered, any doctor or lawyer using the machine would be able to access any document on the system.
What you need is a system that encrypts individual files or at folder level where you grouped many files together, and does not decrypt them until a user with rights to view documents tries to access them. If a doctor logs on to such a system and starts poking around, he would find that legal documents are encrypted.
Even if he were to try to export the legal files to a USB flash drive, they would be useless and unreadable because of the encryption.
As I mentioned earlier, our solution is Kruptos 2 Professional. When a user configures Kruptos with individual password to use this capability, individual files are completely encrypted, and are not decrypted until a user with right master or individual password on and opens the document.
If a user without right password for the file, they would not be able to open any documents. The documents are encrypted using strong, industry standard encryption algorithms – either AES-128 or AES-256.
Any File: With no need to consciously remember to encrypt data that is being processed, enjoy a secure yet natural workflow. Kruptos works for any kind of file.
Any Place: Every file is encrypted no matter where it resides – from creation to storage on any location or medium, even in the cloud. Kruptos supports all major cloud folder providers such as dropbox, google drive, box, icloud, etc.
Any Time: Whenever a file is accessed, edited, moved, duplicated, or touched in any way, the encryption remains in effect. Any changes made are automatically encrypted by Kruptos when you close the file.
Final Thoughts: Full disk encryption Vs file and folder encryption
In the end, both of these security measures are imperative. Full disk encryption is important and a good start, but file and folder encryption is a way to build on that to make the system even more secure and allows to limit data access to authorized applications for specific purposes.
So the next time you are asked, “How are our files protected?” have a discussion about the pros and cons of full disk encryption and file encryption. You may find out you’re not defending against all of the threats to your sensitive data.